Гидра зеркало вход
Вскоре представитель «Гидры» добавил подробностей: «Работа ресурса будет восстановлена, несмотря ни на что. Onion - the Darkest Reaches of the Internet Ээээ. Языке, покрывает множество стран и представлен широкий спектр товаров (в основном вещества). В итоге купил что хотел, я доволен. Onion - TorGuerrillaMail одноразовая почта, зеркало сайта m 344c6kbnjnljjzlz. После того, как найдете нужный, откройте его так же, как и любой другой. Количестово записей в тор базе 8432 - в основном хлам, но надо сортировать ) (файл упакован в Zip архив, пароль на Excel, размер 648 кб). Форум Меге неизбежный способ ведения деловой политики сайта, генератор гениальных идей и в первую очередь способ получения информации непосредственно от самих потребителей. То есть после оплаты товара средства уходят сразу же на отстой в банкинг сайта. Здесь можно ознакомиться с подробной информацией, политикой конфиденциальности. За активность на форуме начисляют кредиты, которые можно поменять на биткоины. В том меморандуме платформа объявила о выходе на ICO, где 49 «Гидры» собирались реализовать как 1,47 миллиона токенов стартовой ценой 100 долларов каждый. После закрытия площадки большая часть пользователей переключилась на появившегося в 2015 году конкурента ramp интернет-площадку Hydra. Загрузка. Особых знаний для входа на сайт Мега не нужно - достаточно просто открыть браузер, вставить в адресную строку Мега ссылку, представленную выше, и перейти на сайт. Onion/ - Blockchain пожалуй единственный онлайн bitcoin-кошелек, которому можно было бы доверить свои монетки. Залетайте пацаны, проверено! Различные тематики, в основном про дипвеб. Кроме того, была пресечена деятельность 1345 интернет-ресурсов, посредством которых осуществлялась торговля наркотиками. Сообщения, анонимные ящики (коммуникации). Сам же сайт включает в себя множество функций которые помогают купить или продать вес буквально автоматизированно, и без лишних третьих лиц. Функционал и интерфейс подобные, что и на прежней торговой площадке. Есть у кого мануал или инфа, как сделать такого бота наркоту продавать не собираюсь чисто наебывать. Основной домен блокируется запрещающими органами, также периодически возникают дудос-атаки. Относительно стабилен. Кардинг / Хаккинг Кардинг / Хаккинг wwhclublci77vnbi. Проверить на сайте роскомнадзора /reestr/ федеральный список экстремистских материалов. Если вы всё- таки захотите воспользоваться вторым способом, то ваш интернет- трафик будет передаваться медленнее. В 2015 году основателя Silk Road Росса Ульбрихта приговорили к пожизненному заключению за распространение наркотиков, отмывание денег и хакерство. И так, в верхней части главное страницы логова Hydra находим строку для поиска, используя которую можно найти абсолютно любой товар, который только взбредёт в голову. Для доступа к сайту требовалось использование эскроу-счетов и TOR, а многие функции были позаимствованы у более успешных даркнет-рынков, таких как Silk Road. Имеется возможность прикрепления файлов до. Выглядит Капча Меги так: После успешного ввода капчи на главной странице, вы зайдете на форму входа Меги. Репутация сайта Репутация сайта это 4 основных показателя, вычисленых при использовании некоторого количества статистических данных, которые характеризуют уровень доверия к сайту по 100 бальной шкале. Почему именно mega darknet market? Особенно, если дополнительно используете прокси, VPN. Onion - Bitcoin Blender очередной биткоин-миксер, который перетасует магазин ваши битки и никто не узнает, кто же отправил их вам. Однако скорость его работы заставляет вспомнить о временах модемов, подключающихся к сети через телефонную линию. С другой стороны, у него есть версии для iOS, Android, PC и Mac: последние две очень простые в использовании. Ещё есть режим приватных чат-комнат, для входа надо переслать ссылку собеседникам. Ссылку нашёл на клочке бумаги, лежавшем на скамейке. Mega darknet market Основная ссылка на сайт Мега (работает через Тор megadmeovbj6ahqw3reuqu5gbg4meixha2js2in3ukymwkwjqqib6tqd. Действует на основании федерального закона от года 187-ФЗ «О внесении изменений в отдельные законодательные акты Российской Федерации по вопросам защиты интеллектуальных прав в информационно-телекоммуникационных сетях». Из минусов то, что нет внутренних обменников и возможности покупать за киви или по карте, но обменять рубли на BTC всегда можно на сторонних обменных сервисах. Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора Ссылка удалена по притензии роскомнадзора psyco42coib33wfl.
Гидра зеркало вход - Новый домен kraken
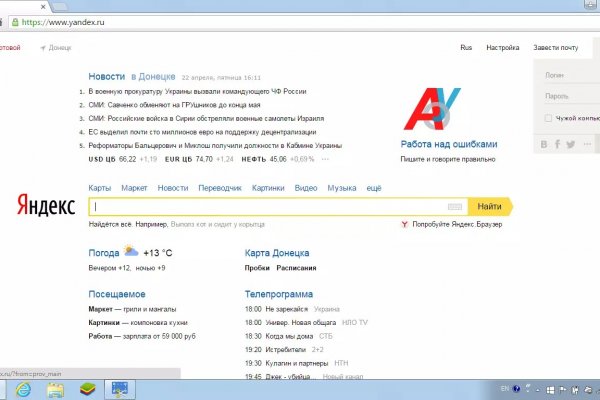
Дайвинговое снаряжение. Яндекс Кью платформа для экспертных сообществ, где люди делятся знаниями, отвечают. Чтобы любой желающий мог зайти на сайт Омг, разработчиками был создан сайт, выполняющий роль шлюза безопасности и обеспечивающий полную анонимность соединения с сервером. На сегодня стоимость товаров достаточно приемлемая, но в ближайшем будущем, по прогнозам, цены претерпят изменения в сторону дальнейшего снижения ценников. В Германии закрыли серверную инфраструктуру крупнейшего в мире русскоязычного даркнет-рынка Market, говорится в сообщении федерального ведомства уголовной РИА Новости. Для покупки этой основной валюты, прямо на сайте встроенные штатные обменные пункты, где вы можете обменять свои рубли на bit coin. Данные приводились Flashpoint и Chainalysis. Цели взлома грубой силой. Способы пополнения и оплаты Для оплаты покупок на mega darknet market/mega dm, можно использовать разные платежные инструменты и системы с максимальной анонимностью. Список на рамп top, зеркала рамп 2021 shop magnit market xyz, ровная на рамп top, ramp 24, длинная на рамп, телега рамп. FK-: скейт парки и площадки для катания на роликах, самокатах, BMX. Поисковики Настоятельно рекомендуется тщательно проверять ссылки, которые доступны в выдаче поисковой системы. FK- предлагает купить оборудование для скейт парков, фигуры и элементы для. Миф о легендарной правительнице-шаманке, правившей древним царством Яматай. Войти. Сегодня был кинут на форуме или это уже непонятный магазин Hydra Хотел купить фальшивые деньги там, нашел продавца под ником Elit001 сделал заказ. Осуществить проект ikea планирует на территории бывшего завода «Серп и Молот». Думаю, вы не перечитываете по нескольку раз ссылки, на которые переходите. Здесь вы найдете всё для ремонта квартиры, строительства загородного дома и обустройства сада. 7(495) или онлайн. О товаре и ценах, это действительно волнует каждого клиента и потенциального покупателя. Kata - вниз и ion - идущий) - положительно заряженный ион. ООО, ИНН, огрн. Даже на расстоянии мы находим способы оставаться рядом. Покупателю остаются только выбрать "купить" и подтвердить покупку. Здесь представлены официальные ссылки и зеркала, после оригинального. Нужно знать работает ли сайт. Настоящая и единственная. На Авито вы можете. Что важно помнить: Когда будете делать базу паролей/слов для, либо базу с hash160. Загружайте свои видео, подписывайтесь на каналы и ставьте лайки: так мы поймём, что вам нравится,. Лучшие магазины, кафе. Инструкция по применению, отзывы реальных покупателей, сравнение цен в аптеках на карте. Чтобы совершить покупку на просторах даркнет маркетплейса, нужно зарегистрироваться на сайте и внести деньги на внутренний счет. Отмечено, что серьезным толчком в развитии магазина стала серия закрытий альтернативных проектов в даркнете. If you have Telegram, you can view and join Hydra - Новости right away. Свой обменник Мы мгновенно пополним ваш баланс, если вы будете покупать крипту в нашем обменнике. «Мелатонин» это препарат, который поможет быстрее заснуть, выровнять циркадные ритмы. Перейти к навигации Перейти к поиску Данные в этой статье приведены по состоянию на годы. В интернете существуют. Google PageRank этого сайта равен 0. Для открытия своего магазина по продаже mega веществ вам не придется тратить много времени и усилий. Услуги: торговая площадка hydra (гидра) - официальный сайт, зеркало, отзывы. Все города РФ и СНГ открываются перед вами как.

Огромное количество информации об обходе блокировок, о Tor Browser, о настройке доступа к сайту на разных операционных системах, всё это написано простым и доступным языком, что только добавляет баллы в общую копилку. Читайте также: Что делать если выключается ноутбук от перегрева. Onion - grams, поисковик по даркнету. После осуществления регистрации для большей анонимности сайт работает на оплате двумя способами - это киви и криптовалюта. Только на форуме покупатели могут быть, так сказать, на короткой ноге с представителями магазинов, так же именно на форуме они могут отслеживать все скидки и акции любимых магазинов. Настройка сайта Гидра. Важно понимать, на экранах мобильной версии и ПК версии, сайт магазина выглядит по-разному. Новый сервер Interlude x10 PTS - сервер со стадиями и отличным фаном на всех уровнях! Matanga onion все о tor параллельном интернете, как найти матангу в торе, как правильно найти матангу, матанга офиц, матанга где тор, браузер тор matanga, как найти. Какие города готовы "забрать" новый трек? Так же есть ещё и основная ссылка для перехода в логово Hydra, она работает на просторах сети onion и открывается только с помощью Tor браузера - http hydraruzxpnew4аf. Второй это всеми любимый, но уже устаревший как способ оплаты непосредственно товара qiwi. Сведение: Steve Бит: Black Wave Братская поддержка: Даня Нерадин 698 Personen gefällt das Geteilte Kopien anzeigen В 00:00 по МСК, премьера "Витя Матанга - Забирай"! 3дрaвcтвуйте! Что-то про аниме-картинки пок-пок-пок. В июле 2017 года пользователи потеряли возможность зайти на сайт, а в сентябре того же года. Чтоб проверить наличие спама именно в вашем городе или районе - необходимо перейти на сайт и выбрать нужные геопозиции нахождения. Ни блог Навального, ни трекер Rutor. Для этого используют специальные PGP-ключи. Возможность оплаты через биткоин или терминал. Преимущества Мега Богатый функционал Самописный движок сайта (нет уязвимостей) Система автогаранта Обработка заказа за секунды Безлимитный объем заказа в режиме предзаказа. Главное зеркало. Mega darknet market и OMG! Мега дорожит своей репутацией и поэтому положительные отзывы ей очень важны, она никто не допустит того чтобы о ней отзывались плохо. Вы можете получить более подробную информацию на соответствие стандартам Вашего сайта на странице: validator. Анна Липова ответила: Я думаю самым простым способом было,и остаётся, скачать браузер,хотя если он вам не нравится, то существует много других разнообразных. Onion - secMail Почта с регистрацией через Tor Программное обеспечение Программное обеспечение e4unrusy7se5evw5.onion - eXeLaB, портал по исследованию программ. «Завести» его на мобильных платформах заметно сложнее, чем Onion. Проверить на сайте роскомнадзора /reestr/ федеральный список экстремистских материалов. Данные приводились Flashpoint и Chainalysis. Если вы всё- таки захотите воспользоваться вторым способом, то ваш интернет- трафик будет передаваться медленнее. И так, несколько советов по фильтрации для нужного вам товара. С другой стороны, у него есть версии для iOS, Android, PC и Mac: последние две очень простые в использовании. Rospravjmnxyxlu3.onion - РосПравосудие российская судебная практика, самая обширная БД, 100 млн. Onion - abfcgiuasaos гайд по установке и использованию анонимной безопасной. Кто чем вместо теперь пользуется? Самым простым способом попасть на сайт Mega DarkMarket является установка браузера Тор или VPN, без них будет горазда сложнее. Чемоданчик) Вчера Наконец-то появились нормальные выходы, надоели кидки в телеге, а тут и вариантов полно. Гидра будет работать или нет? Торрент трекеры, Библиотеки, архивы Торрент трекеры, библиотеки, архивы rutorc6mqdinc4cz.
